The question nobody is asking about Mythos is the one that matters most: what happens when thousands of exploitable conditions hit the ecosystem and the CVE pipeline can't process them fast enough for your tools to see them?
That's not hypothetical. Mythos Preview has already found thousands of high- and critical-severity vulnerabilities across every major operating system and browser. It found a 16-year-old bug in FFmpeg's H.264 codec, a media processing library embedded in virtually every application that handles video. It chained together four vulnerabilities in Firefox's JavaScript engine to escape both the renderer and OS sandboxes. That code has been running on your endpoints for years. Every fuzzer and human reviewer in the world missed it.
Within 48 hours of the Glasswing announcement, the industry's response followed a predictable playbook. Patch faster. Map compensating controls to known CVEs. Push signature updates. Automate remediation workflows. Build surge capacity. Every one of those responses depends on the same thing: a CVE existing before anyone can act.
Mythos just produced thousands of findings. Fewer than 1% have been patched. The rest are sitting in a responsible disclosure queue, waiting for CVE assignment, vendor triage, and patch development. Meanwhile, the exploitable conditions those findings describe exist on your endpoints right now. As other frontier models are released with similar capabilities, and perhaps less restrictive release, this problem will only get worse. If past is prologue, 6 months after Mythos release, we’ll see comparable capabilities in open source models.
The industry is debating how to close the gap between patch release and patch deployment. That's a real problem. But it's the second problem. The first problem is the gap between exploitable condition and CVE existence. And that gap just went from an inconvenience to a structural failure mode.
The CVE system was designed for a world where humans found vulnerabilities at human speed. That world ended on April 7.
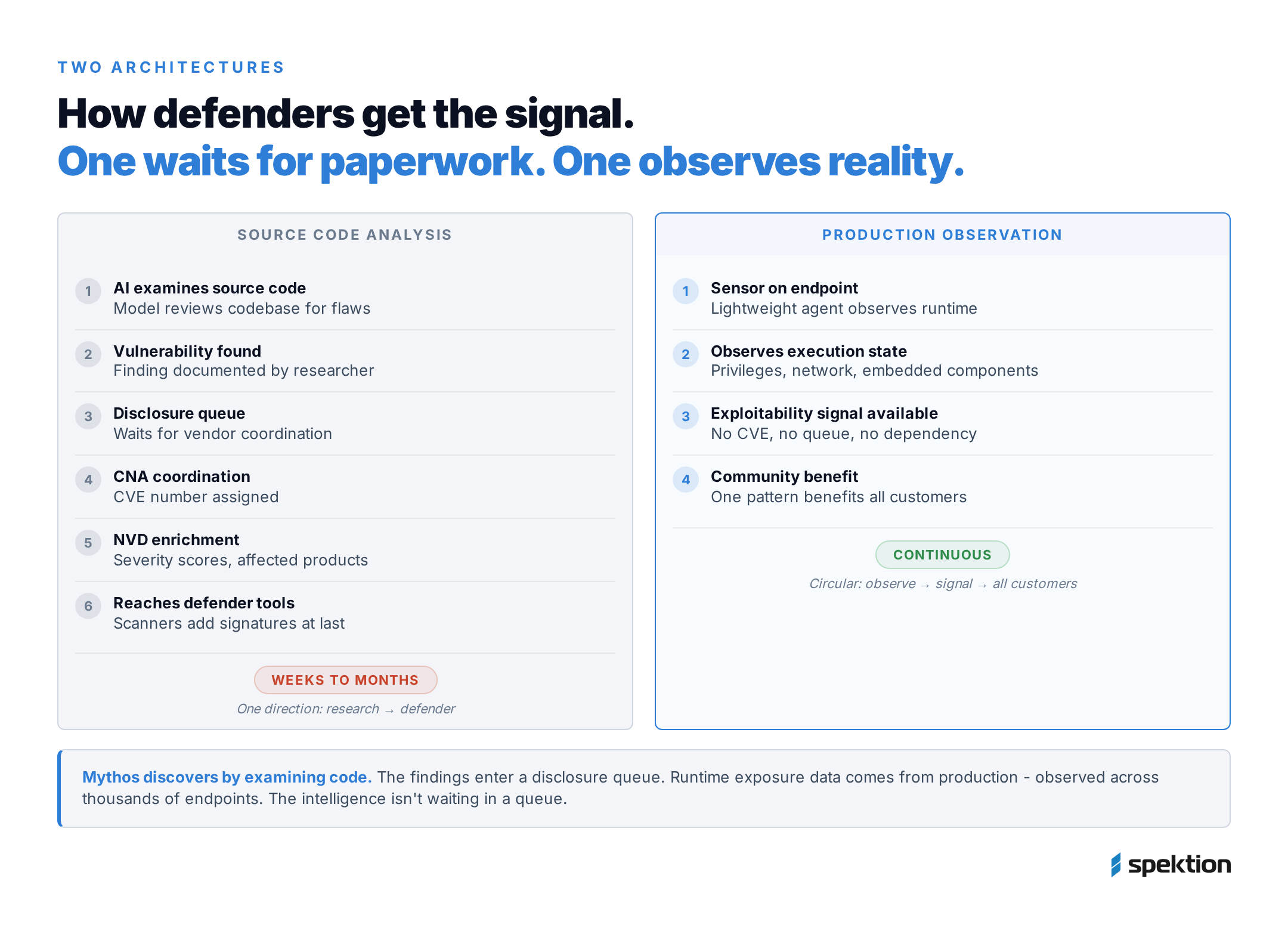
The pipeline works like this: vulnerability discovered, filed with a CNA, enriched by NIST's NVD with severity scores and affected product data, then ingested by downstream tools. Scanners add signatures. RBVM platforms prioritize. Compensating controls map defenses. Every step takes time. And the chain was already failing before Mythos.
By March 2025, the NVD backlog hit 25,000 unprocessed CVEs. Nearly half of all CVEs added in the prior year were sitting in "awaiting analysis" status: no severity scores, no affected product lists, no actionable data. NIST's response was to mark every pre-2018 CVE as "Deferred," which is a polite way of saying they stopped trying to process them.
VulnCheck's 2026 Exploit Intelligence report found that 29% of known exploited vulnerabilities in 2025 were exploited on or before the day their CVE was even published. Not before the patch. Before the CVE. Attackers aren't waiting for the disclosure pipeline to finish. They're moving while it's still loading.
Now add Mythos. Thousands of new critical findings entering a pipeline that was already 25,000 records behind. But here's the part that hasn't gotten enough attention: Mythos is exceptionally good at finding vulnerabilities. There is no evidence it can rewrite the software to fix them.
Additionally, there are legitimate CVEs that never get formally accepted during the disclosure policy and end up released publicly, like the recent Bluehammer local privilege escalation exploit that was released by a researcher after reported frustration with Microsoft’s handling of the diclosure process. As vulnerability discovery capabilities available to researchers improve, these episodes of non-CVE disclosures are likely to increase.
Discovery got automated and accelerated. Remediation didn't.
The patches still require human developers to write, test, and release. The queue grows on one side while the processing capacity stays fixed on the other. Even the platforms that promise to bridge the patch gap, the ones mapping compensating controls to known CVEs, need the CVE to trigger the workflow. No CVE, no mapping. No mapping, no mitigation.
The industry's Mythos response assumes the CVE pipeline will deliver signal fast enough to act on. The pipeline's own track record says otherwise.
A CVE is a label. It's not the vulnerability. It's the bureaucratic acknowledgment that someone documented one.
The vulnerability is a runtime condition. Code that can be exploited, executing in production, with the privileges and network exposure to make exploitation meaningful. That condition exists on the endpoint whether or not someone has filed paperwork about it.
Mythos didn't create new vulnerabilities last week. It found conditions that already exist on your endpoints, some for nearly two decades. The FFmpeg H.264 bug has been exploitable since 2010. The OpenBSD SACK flaw since 1998. Your endpoints didn't change on April 7. What changed is that someone finally documented the conditions. And most of those documents haven't even entered the CVE pipeline yet.
For findings that get CVEs quickly, the existing playbook applies, however slowly. But for findings that sit in the disclosure queue for weeks, or straddle the line between vulnerability and misconfiguration and may never get a formal CVE at all, the playbook breaks completely. Your scanner can't find what it doesn't have a signature for. Your compensating controls engine can't map defenses against a CVE identifier that doesn't exist.
This is the CVE-shaped hole. If your entire exposure model depends on a CVE existing before you can see risk, you are structurally blind to every exploitable condition that hasn't been cataloged yet. That was always a manageable limitation when humans found vulnerabilities at human speed. It is not manageable when an AI model produces thousands of critical findings in weeks and the labeling system takes months to process them.

That gap just became the widest it has ever been.
Next time a vendor tells you they can prioritize your exposure, ask one question: what happens when the CVE doesn't exist yet?
There's a different way to see exposure. Instead of waiting for a CVE to tell you something is vulnerable, you observe the condition directly.
Runtime exposure data watches what's actually happening on the endpoint: what is executing right now, in production, with real privileges and real network exposure. Is the code actually running, or just installed and dormant? Is the process running with elevated privileges? Is it accepting inbound network connections? Is a vulnerable library embedded inside another application where a traditional scanner can't even see it?
Those answers don't require a CVE or an NVD enrichment record. The exploitable condition is observable the moment the software runs.
That embedded component point matters more than most people realize. When Mythos finds a vulnerability in a library like FFmpeg, the CVE will reference FFmpeg. But on your endpoints, that library isn't running as "FFmpeg." It's compiled into dozens of other applications, invisible to any scanner checking installed software versions. Runtime telemetry sees the vulnerable code executing inside the process, regardless of how it was packaged.
The vulnerabilities Mythos found were exploitable for years, sometimes decades, before anyone documented them. The CVEs are new. The exposure is not. In a post-Mythos world, the volume of exploitable conditions without CVEs will spike. The only tools that remain useful across all of those scenarios are the ones that don't need the CVE as their starting point.
That's the problem we built Spektion to solve. Runtime exposure data tells you what's exploitable in your environment, whether there's a CVE for it or not. One sensor, observing execution state, privilege levels, network exposure, and embedded components continuously. And because attackers will use the same class of models to accelerate vulnerability discovery and exploitation, defenders need an exploitability data plane that AI agents can consume at machine speed. The automation layer matters, but it's only as good as the signal it's acting on. An agent moving at machine speed on CVE-dependent data is fast and blind. An agent moving at machine speed on runtime exploitability data can act on conditions that don't have CVEs yet.
There's a difference worth noting in how this data is produced. Mythos discovers vulnerabilities by examining source code. That's powerful, but it's a research pipeline: findings enter a disclosure queue, wait for CVE assignment, and eventually reach defenders. Runtime exposure data comes from production environments, observed across thousands of endpoints running real workloads. When one environment reveals an exploitable pattern, that observation benefits every organization in the community. The intelligence isn't waiting in a disclosure queue. It's already in the data plane, generated by the same endpoints it protects.
Mythos will improve software security over the long term. The codebases that Glasswing partners are auditing will come out stronger. That's genuinely good. The short-term stress on defenders is a different story, and the organizations that come through it best will be the ones that understood their exposure before the CVEs arrived.
Compensating controls have a role in this response, but it's the last line of defense, not the primary one. Reactive mitigations applied after a vulnerability is known, designed to buy time until a patch deploys. Valuable, but fragile. The same AI capabilities that let Mythos discover and weaponize vulnerabilities will be used to find paths around those controls.
You can't block what you can't predict. But you can eliminate the conditions that make it work.

The more durable defensive posture is pre-attack: eliminating the conditions that make exploitation possible in the first place. If a service is running as root but doesn't need root privileges, reducing it to a standard user account eliminates privilege escalation as an exploitation path for every vulnerability in that service, current and future, disclosed and undisclosed. That's not a response to a specific CVE. That's a permanent reduction in exploitability. These configuration-level changes shrink exploitability before an attacker ever arrives, and they don't depend on knowing the specific vulnerability in advance.
That's the shift runtime exposure data enables. Not "here's a CVE, here's a control to block it." Instead: "here's what's running, here's what's exposed, here's what you can change right now to reduce the blast radius of whatever comes next."
The CVE-shaped hole isn't a Mythos problem. It's a structural property of every tool that uses CVE as its index key. Mythos just made it measurable.
1. How much of your exposure visibility depends on a CVE existing? If your scanner, your RBVM, and your controls mapping all require a CVE as the input, you have a single point of failure in your exposure model.
2. Can you see what's actually running, with what privileges, and what's network-reachable, independent of whether a vulnerability has been cataloged? If not, the Mythos disclosure wave will hit your environment before it hits your tooling.
3. When thousands of new critical findings enter the pipeline simultaneously, how do you decide what to address first? Severity scores won't exist yet. Exploit intel won't exist yet. The only prioritization signal that works before the CVE pipeline catches up is the one you can observe directly from the endpoint.
If you don't know the answers, we can show you in 30 minutes what your CVE dependency actually looks like.
The CVE system isn't going away. It still matters. But treating it as a prerequisite for seeing risk was always a fragile assumption. Mythos just made that fragility impossible to ignore.