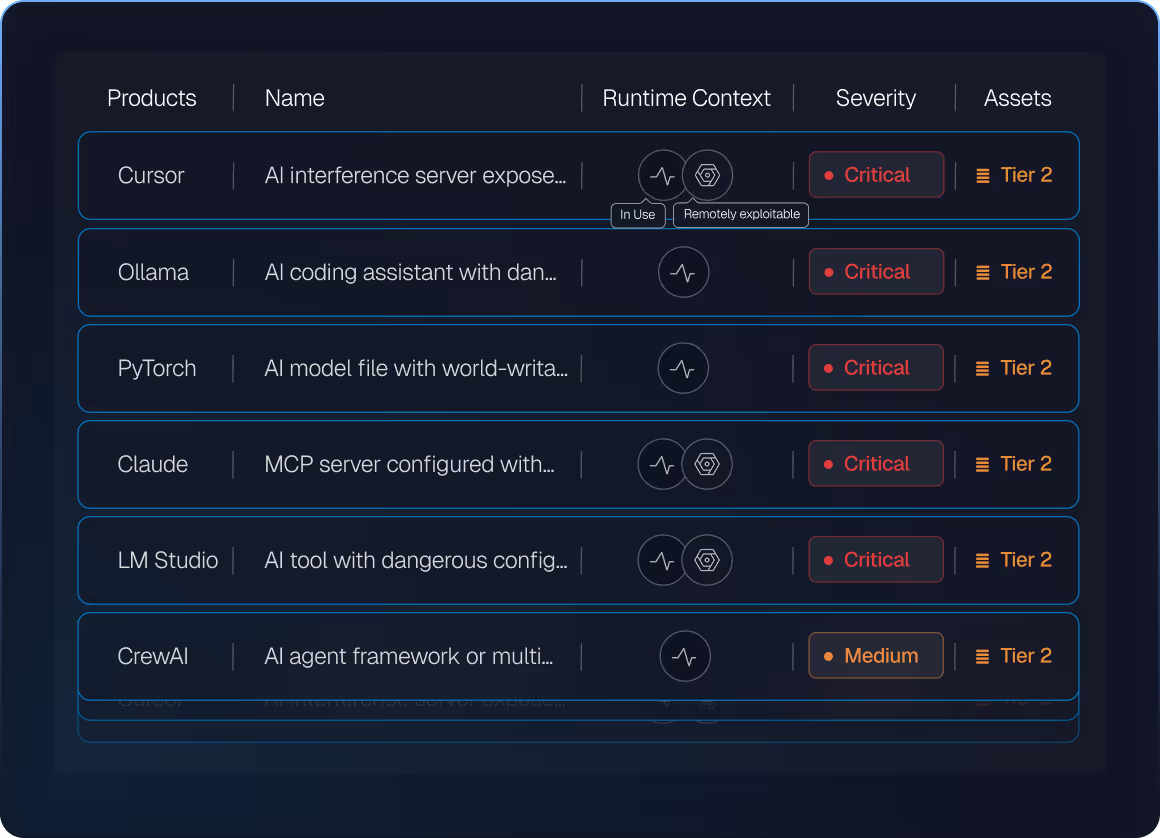
Endpoints running unsanctioned AI tools
Observed in early Spektion deployments.

More AI workloads than security teams expect
Runtime discovery baseline across early deployments.

Into AI agents, MCP servers, or AI-generated executables in your current stack
VM tools, scanners, and EDR cannot detect these workloads.

Of AI runtime behavior is detected by traditional tools
No traditional tool observes what AI workloads are actuallly doing on endpoints.