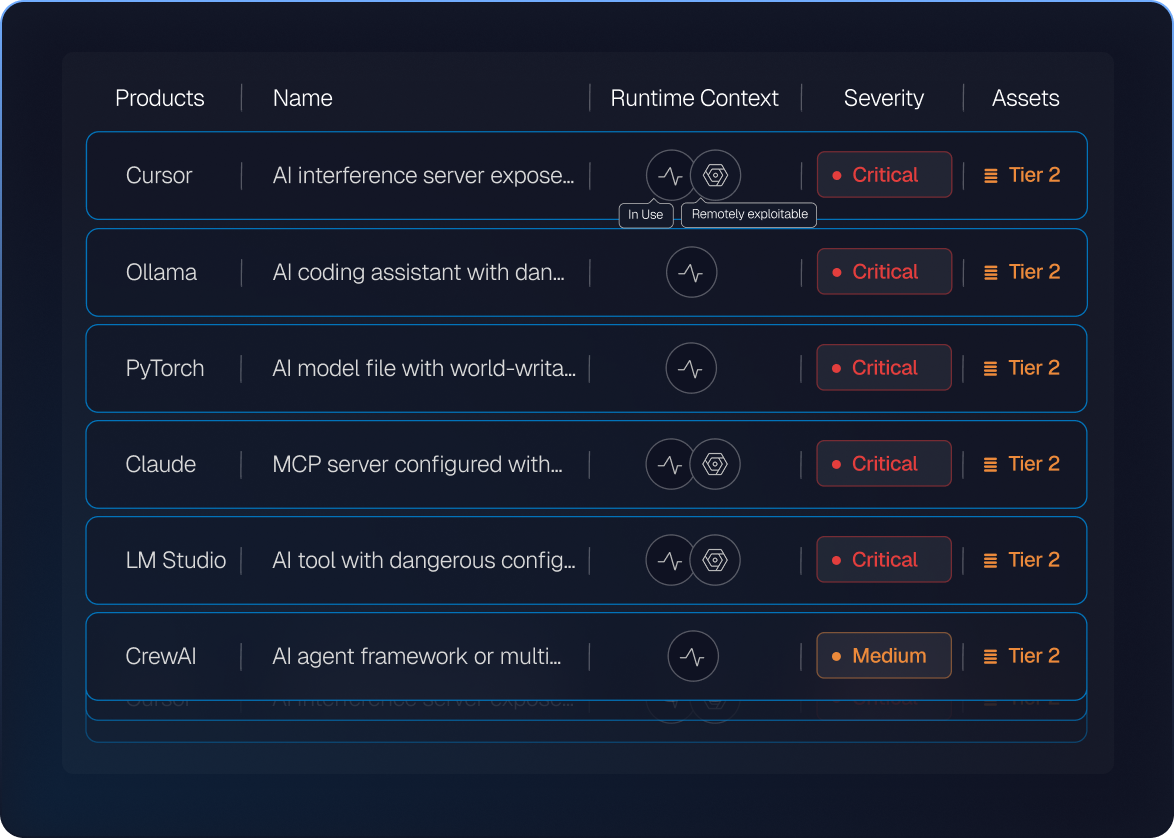
Applications with exploitable flaws that had no CVE
Spektion runtime research across widely deployed software.
Source: Spektion Research

Recent supply-chain attack campaigns with no CVE
Industry incident analysis across recent documented campaigns.
Source: Industry incident analysis

In AI-generated workloads on endpoints
High-risk runtime behavior identified — high privilege, executable memory, listening on open port.
Source: Spektion runtime research