Runtime evidence turns CVE noise into clear action
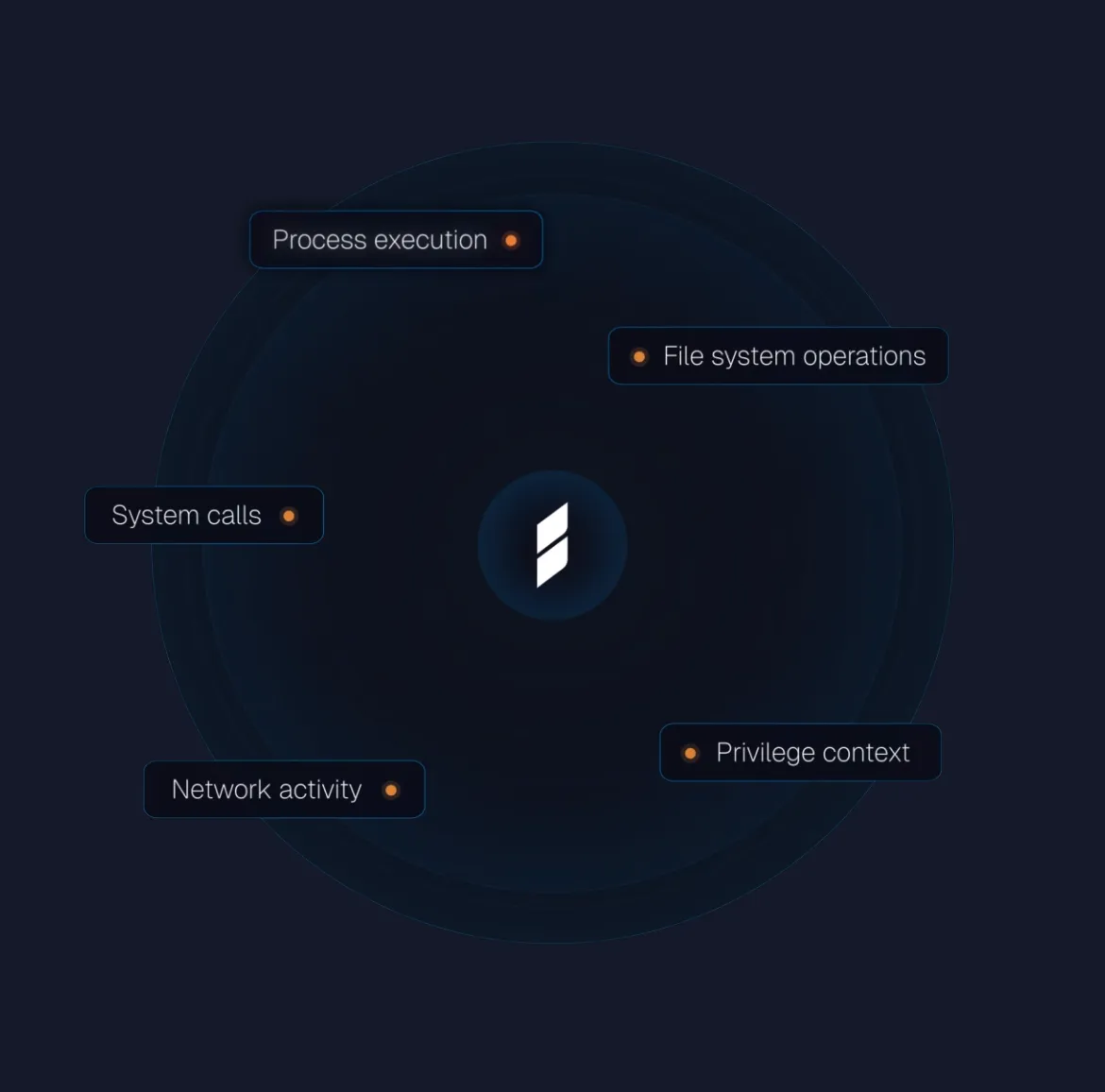
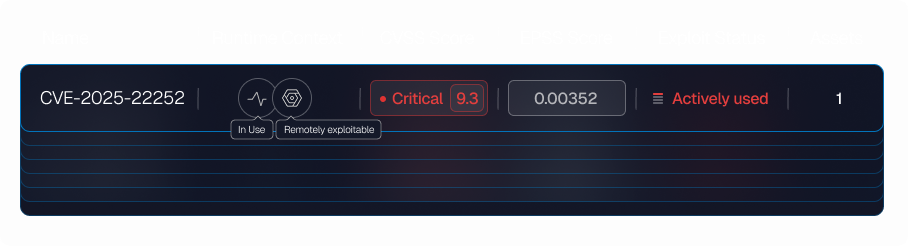
Observing software at runtime replaces static vulnerability findings with continuous execution evidence—what’s running, what’s exposed, and what’s truly exploitable. Instead of working from CVE lists and scan snapshots, you work from live execution evidence that separates real risk from theoretical findings.
That lets your team:
Focus on exploitable CVEs in your environment, not just vulnerable software

Surface exploitable weaknesses that CVE databases never cover
Cut remediation cycles by focusing only on what's running and exposed

Apply targeted controls before patches are available