In many organizations, “vulnerability management” has become a catch-all term for finding and fixing software flaws. In practice, what most teams actually do is patch management—rolling out vendor patches and software updates on a fixed schedule, usually driven by IT operations.
While patching is essential, it is not the same as vulnerability management. Treating them as interchangeable leaves critical exposures unaddressed, especially when attackers move faster than patch cycles.
In this article, we’ll clarify how patch management and vulnerability management differ, why confusing the two leaves dangerous gaps, and what a risk-based approach to vulnerability management looks like.
Patch management is an IT-driven process focused on keeping systems current with vendor fixes by acquiring, testing, and installing updates for software and systems. It’s all about staying up-to-date.
In practice, patch management typically looks like this:
The challenge? Patch management is schedule-driven, not risk-driven. Teams focus on capacity to patch, not necessarily what addresses essential risks to the business. For example, suppose a new RCE is disclosed the day after a scheduled patch cycle; patching on a set schedule means it sits unaddressed until the next maintenance window, barring an emergency change, leaving systems exposed despite “being up to date.” There is only so much engineering capacity and political capital available to field such emergency changes.
Limitations of patch management include:
Patch management is essential but incomplete. It keeps systems current, but by itself it doesn’t provide a risk-based view of which exposures matter most, and that’s where vulnerability management steps in.
Vulnerability management is broader and more strategic than patch management. It’s about continuously identifying and reducing the actual risk of vulnerabilities being exploited, not just managing the capacity available to apply patches.
The lifecycle typically includes:
Analyst frameworks like Gartner’s Continuous Threat Exposure Management (CTEM) model emphasize this type of continuous cycle as the foundation of modern vulnerability management programs. If you have a CTEM program or are planning on implementing one, check out this article: CTEM Program Visibility Gaps and How to Close Them at Runtime.
In summary, unlike patch management, vulnerability management doesn’t stop at “is there a patch?” It asks, “Is this vulnerability exploitable, and what’s the fastest, most effective way to reduce the risk?”
Here’s how the two approaches differ side by side.
The limits of patching become clear when the risk isn’t tied to a vendor fix. Some of the most dangerous exposures—from zero-days to configuration drift to even exploitable issues in homegrown tools—have no patch available, leaving organizations exposed, unless they take additional steps.
True vulnerability management fills that gap with:
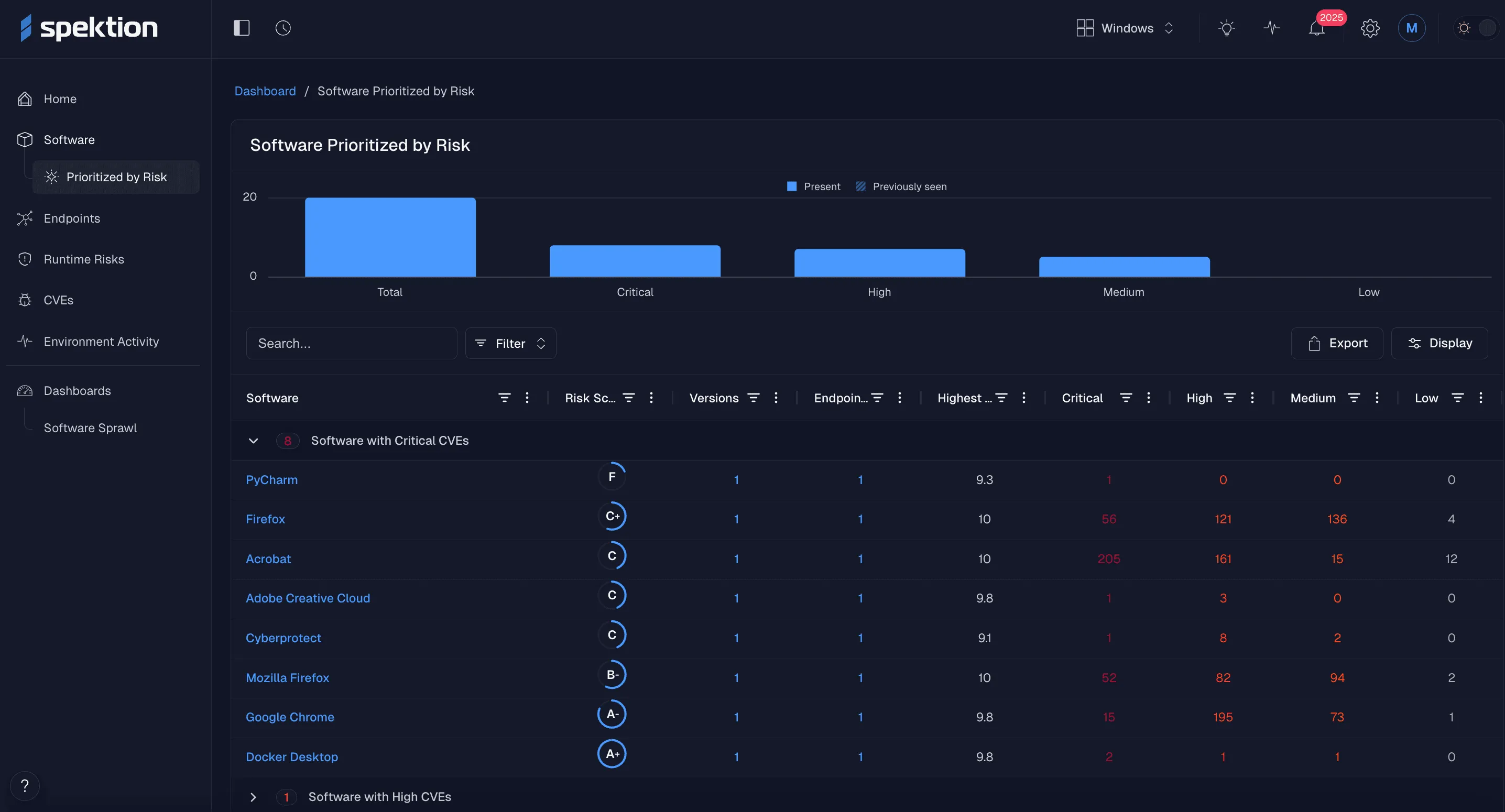
The gap between patch management and vulnerability management is where most organizations struggle. Patching keeps systems current, but it doesn’t answer the bigger question: which risks actually matter right now? That’s where Spektion steps in.
With Spektion’s runtime vulnerability management, security and IT teams gain continuous, contextual visibility into installed software, going far beyond what patching alone can deliver. Here’s how that visibility changes the game:
The result isn’t just faster patching. It’s smarter, risk-driven remediation that helps teams break free from the limitations of the patch cycle.
For security leaders, the difference between patch management and vulnerability management isn’t just semantics. It’s the difference between staying stuck on the CVE treadmill and actually reducing exploitable risk. Patch management is how IT teams address vulnerabilities prioritized by security. Vulnerability management is how security teams not only prioritize vulnerabilities based on risk, but also address the residual risk for what can’t be patched.
Most security teams think they have vulnerability management, when in reality, they have a patching process. Without validated risk data, security can’t tell IT which vulnerabilities truly matter, and IT can’t prioritize patches based on exploitation risk.
Organizations that move beyond patch cycles to risk-driven vulnerability management gain a measurable edge: fewer wasted cycles, faster remediation of what matters, and proactive protection controls that keep pace with attackers rather than vendors.
Spektion enables this by prioritizing vulnerabilities based on intelligence from the most relevant source—your own environment—rather than relying solely on generic data feeds.
That’s the shift Spektion enables, by feeding both IT and security teams the same prioritized intelligence so every patch, mitigation, or removal can be applied where they reduce real-world exposure the most.
###
If you’re ready to break free from the patch cycle and move toward risk-driven vulnerability management, see how Spektion can help: