Real-Time Visibility Into Third-Party Software Risk
Third-party software is part of your attack surface, but your current tools can't see it. Spektion shows how third-party software behaves in your environment, beyond CVEs and vendor questionnaires.

Why Vulnerability Management and Third-Party Risk Management Miss Software Risk
Vulnerability Management (VM) and Third-Party Risk Management (TPRM) tools are useful, but they only cover part of the picture. Vulnerability Management tools stop at known CVEs. Third-Party Risk tools stop at questionnaires and certifications. Neither shows how third-party software behaves in your environment, where the real risk lives.
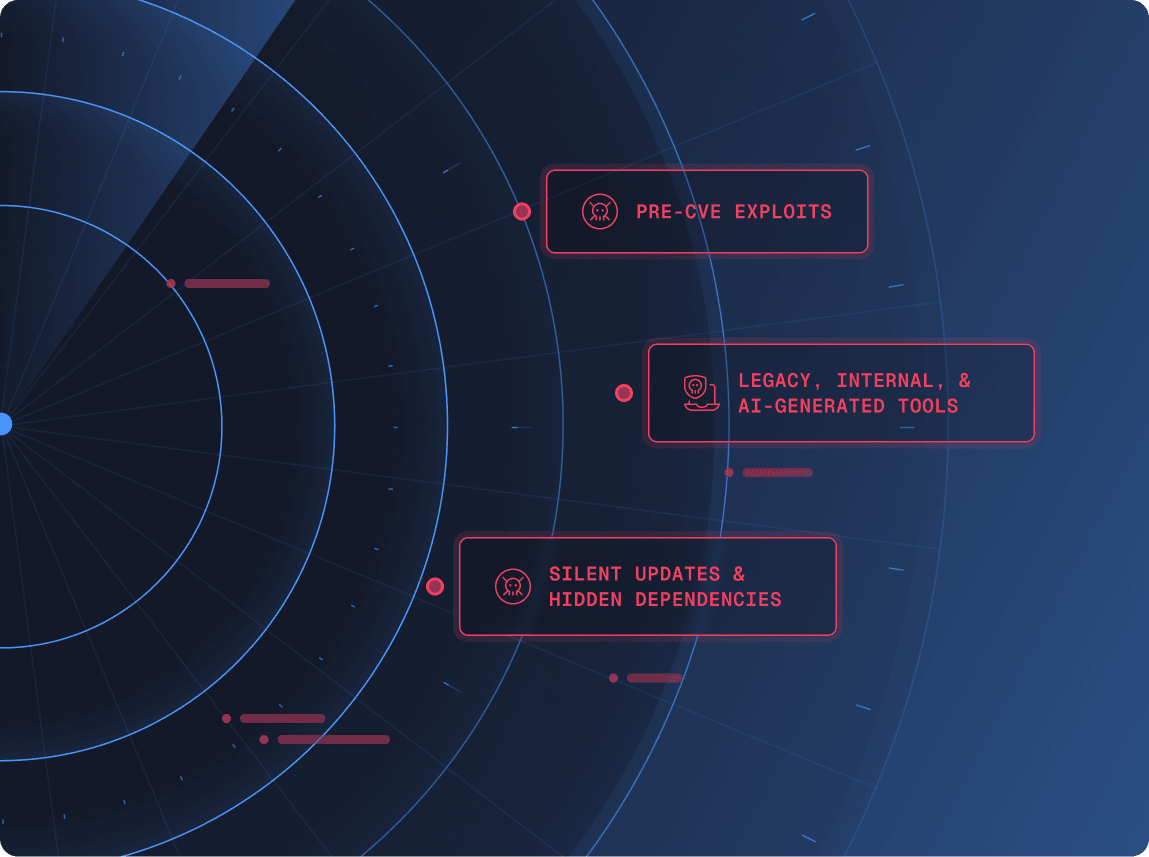
Both leave major gaps
- Pre-CVE exploits attackers use long before disclosure
- Legacy, internal, and AI-generated tools that will never receive CVEs
- Silent updates and hidden dependencies that slip past security review
Those Gaps Leave You Exposed

of organizations with poor third-party visibility suffered a breach in the past year

of breaches in 2025 involved third-party software

of security leaders are concerned about third-party component risk
Runtime Visibility Into Third-Party Software Risk Closes the Gap
Spektion closes the gap with runtime visibility into third-party software behavior. We help you assess third-party software risk by showing what’s exploitable right now, with evidence from your environment, so your vulnerability management and third-party risk programs finally have the data they’ve been missing.
How Runtime Visibility Reduces Risk
1. Discover what's running
Build a live inventory, including shadow and unmanaged tools.
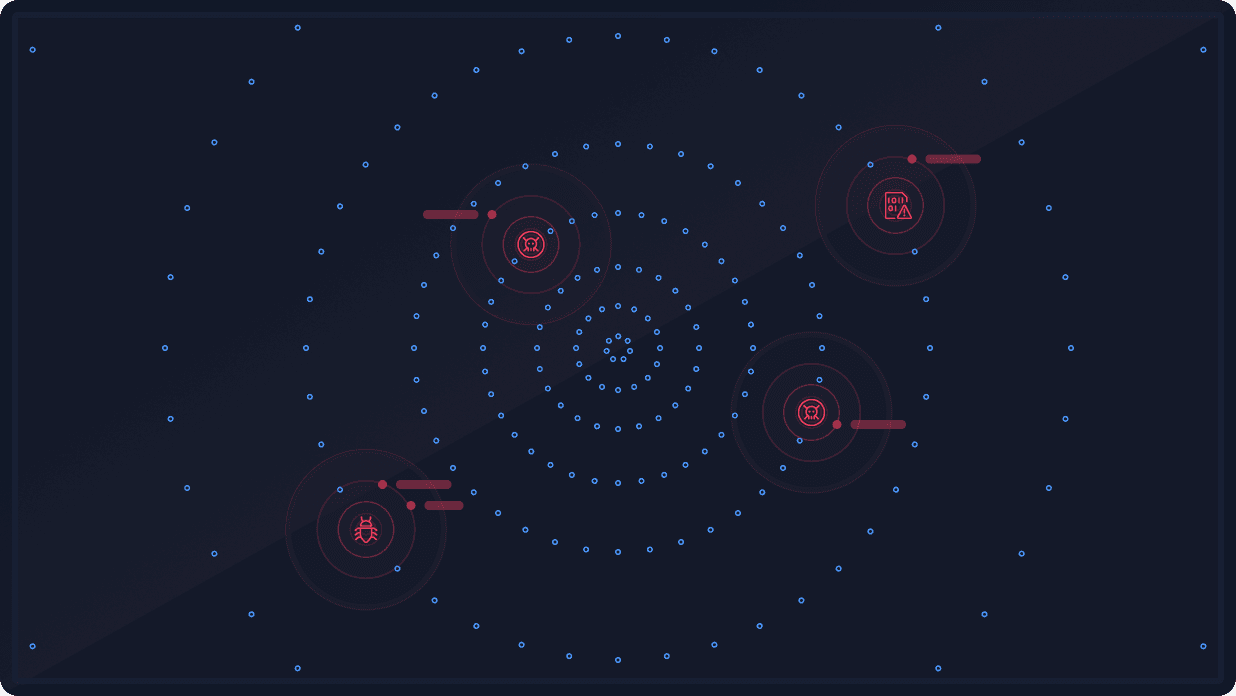
2. Detect risky behavior
Spot privilege escalation, injection, hijacked updaters, and insecure network activity.
3. Score with evidence
Prioritize with runtime data enriched by CVE, CWE, ATT&CK, and threat intel.
4. Apply compensating controls to proactively address risk
Contain unpatchable risk and reduce exposure in real time.
Use Cases Across the Software Lifecycle
Spektion provides value at every stage of software adoption and use:
Compliance as a Byproduct
Audit requirements don’t go away, but Spektion makes compliance easier by turning runtime evidence into audit-ready data.
With Spektion, you get:

Compliance isn’t why leaders choose Spektion. It’s what happens naturally when runtime evidence powers your program.
Why Security Leaders Choose Spektion
Third-party software risk has lived between silos for too long, until now.
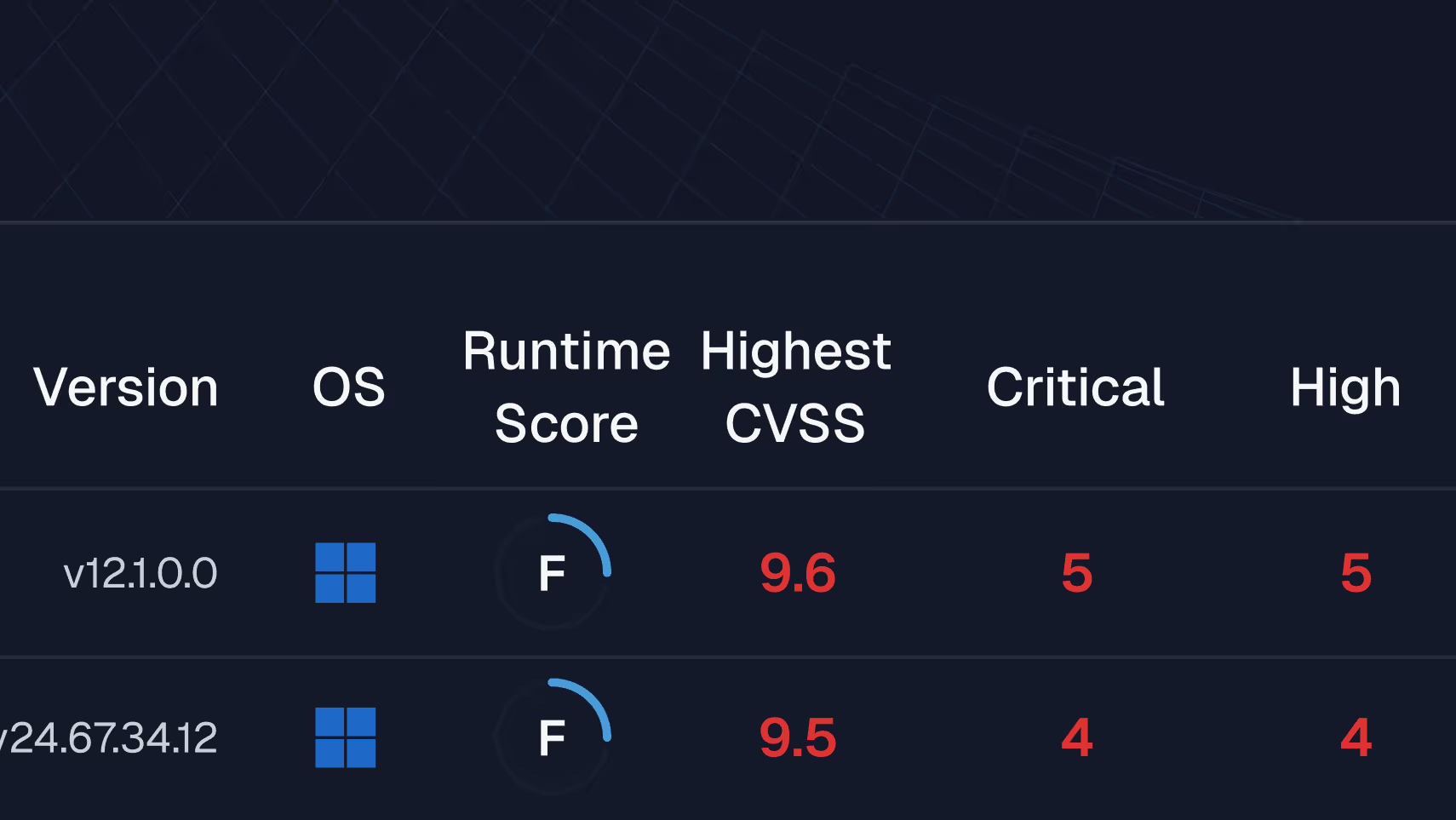
Old way
With Spektion
The impact: Organizations using runtime visibility reduce exploitable exposures by double digits in weeks, cutting both operational risk and wasted patching effort.