Runtime Assurance for AI-Coded Apps
Spektion detects runtime risks from known and unknown internal tools, AI-enabled and low-code citizen development, and third-party software in your environment in real-time.
Software Exposure Is Growing Faster Than Teams Can Manage
Spektion is how vulnerability management teams can respond at speed and scale to software exploitation risk without stopping employees from building with AI. Our tool passively monitors all your software at runtime, showing a live view of risk regardless of how an application was built.
AI-Enabled Development Is Growing Your Attack Surface
AI and low-code tools make it easy for anyone in your organization to quickly build and deploy applications without security safeguards, increasing exploitation risks through:


Spektion Gives You Runtime Visibility Into AI-Written and Low-Code Apps In Your Environment
Spektion’s Runtime Vulnerability Management (RVM) technology can detect and prioritize exploitable vulnerabilities in the AI-coded apps that already live in your environment, even in applications you don’t manage.
Here's how:
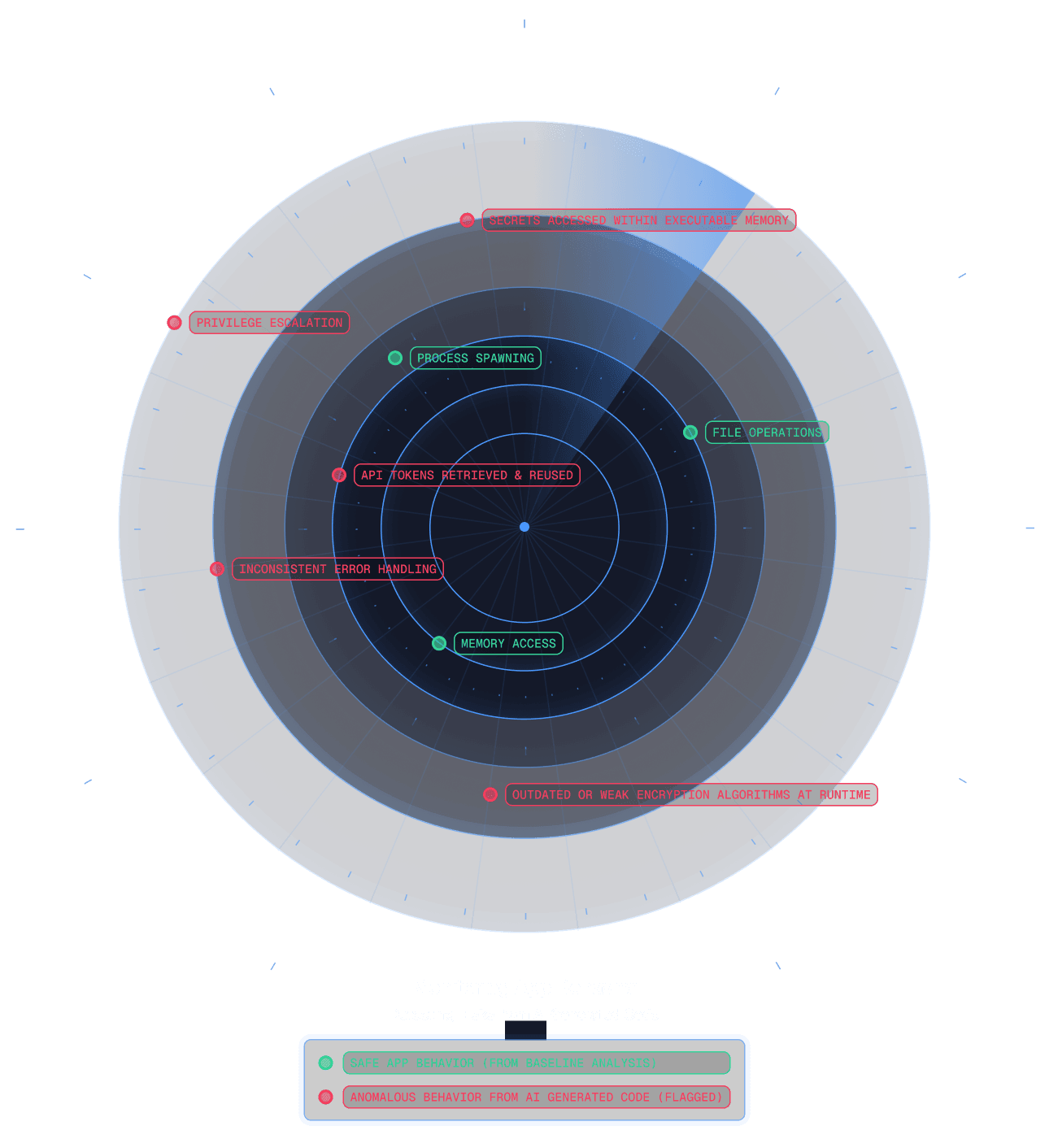
1. A lightweight, passive, agent monitors your systems' runtime environment:
RVM automatically learns what normal looks like for every application in your environment. Zero manual tuning required.

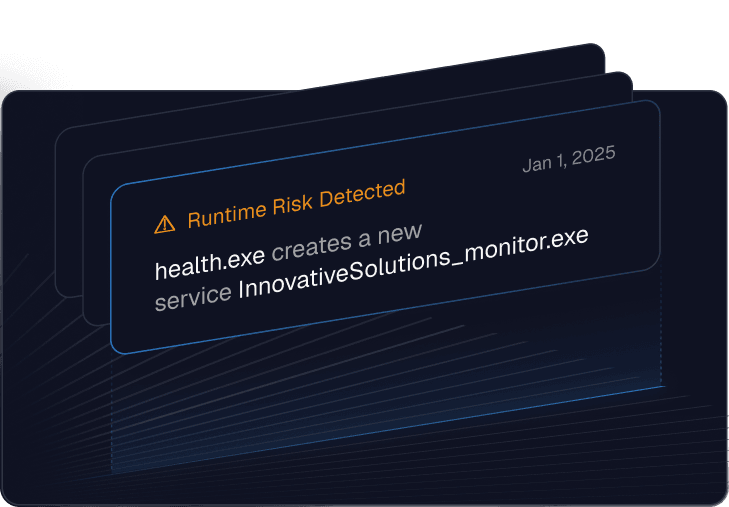
2. Flags deviations that indicate risk:
Including unusual privileged operations or network access, memory access, elevated privileges, exploitation signals, and other suspicious runtime behaviors.
3. Prioritize
Spektion provides a risk score that shows real risk in the context of your environment when CVSS scores aren’t available.
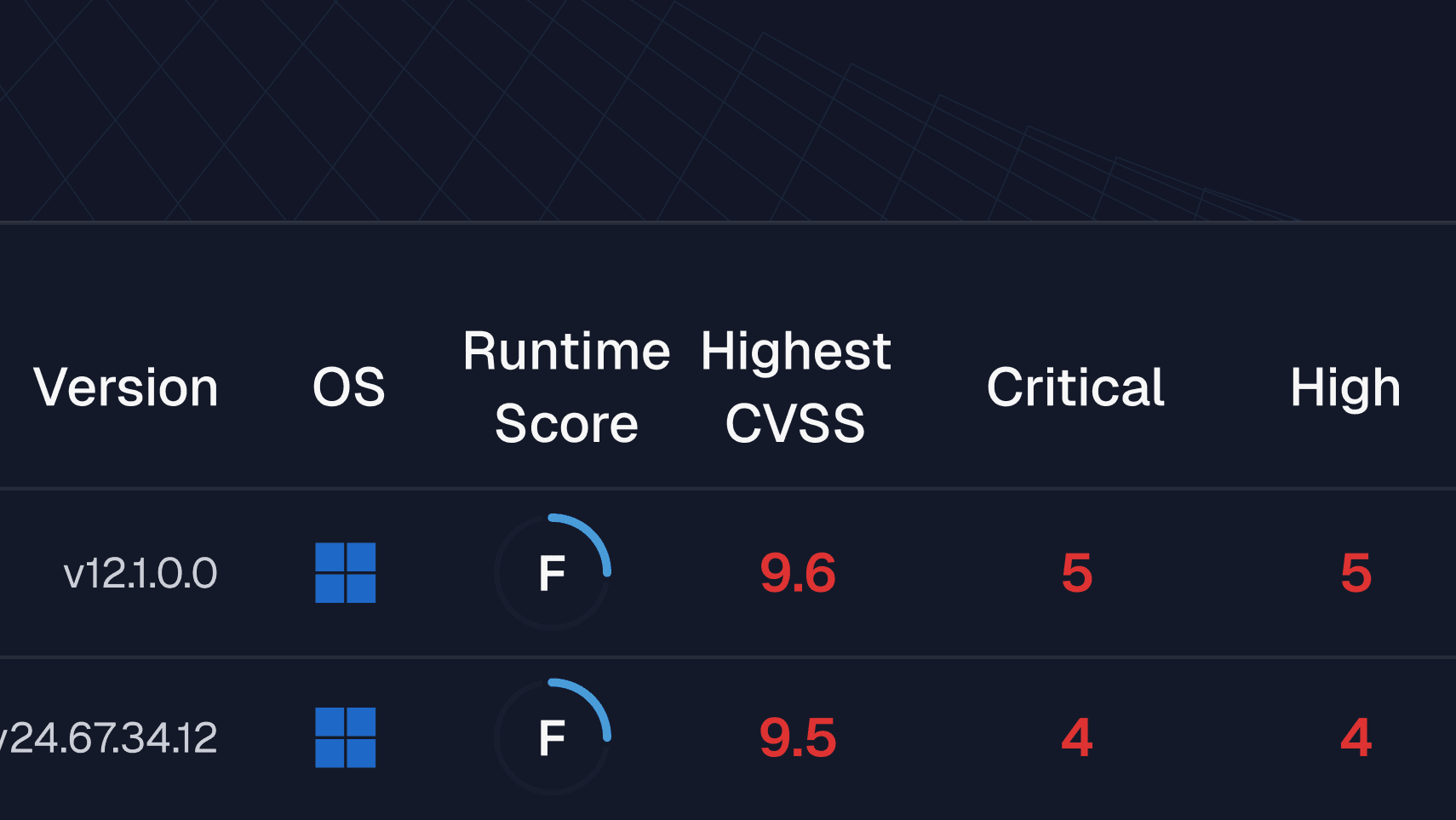
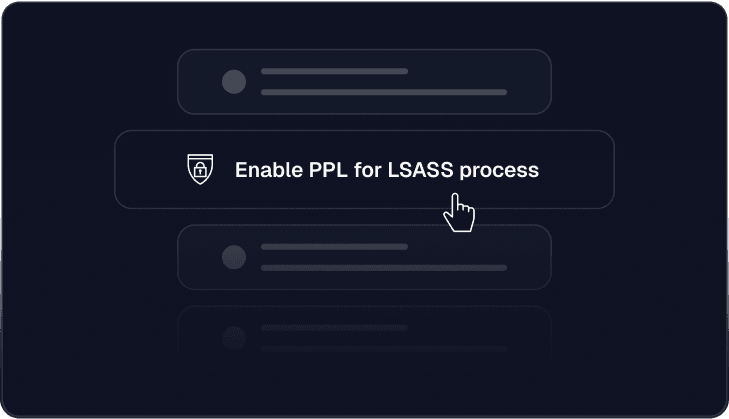
4. You get a prioritized risk view.
Including remediation next steps and options beyond patching.
Spektion delivers continuous runtime insight that’s easy to implement and provides immediate value, helping CTEM programs focus on what’s exploitable and actionable in real time.
Automated App Discovery and Vulnerability Management




Detect AI-Coded Vulnerabilities That Scanners Miss
Spektion helps you transform vulnerability management from a reactive, signature-based process into a toolkit for managing high-tempo software risks, shadow IT, and vulnerabilities without needing access to source code.
Manage AI-Driven Risk Without Adding Headcount or Blocking Innovation
Spektion detects risky behavior from all software running in your environment, not just the apps IT are aware of. This includes AI-generated code, low-code tools, internal scripts, open-source components, and unsanctioned shadow IT.
Whether software was written by a senior developer in your organization, generated in a Copilot prompt, or supplied by a third-party provider, Spektion sees signs of real exploitation before CVEs even exist, including:
- LLM-coded apps retrieving secrets with over-permissioned access.
- Business apps unexpectedly accessing sensitive memory regions.
- Citizen-built dashboards initiating insecure outbound connections.
- AI-generated services requesting elevated privileges.
- Runtime behaviors that resemble known malware patterns.
By combining behavioral signals with environmental context, Spektion gives you focused risk intelligence, so you can act on what’s actually dangerous, not just what scanners flag as “vulnerable.”